Die Entwickler der beliebten Opensource Firewalllösung pfSense, haben das Update in Version 2.2.2 freigegeben. Damit beheben sie einige kleinere Fehler und 2 Low Level Sicherheitsprobleme. Die Security Fixes umfassen ein Problem das bei der Verwendung von IPV6 auf dem WAN Port, bestehen kann. In schlimmsten Fall kann ein Angriff / Fehler dazu führen, dass die IP-Adresse kurzfristig verloren geht. Der zweite Fix betrifft diverse OpenSSL Probleme, die laut den Entwicklern kaum ausgenutzt werden können und im schlimmsten Fall zu einem Denial of Service Angriff führen.
Release zu den Security Fixen
- FreeBSD-SA-15:09.ipv6: Denial of Service with IPv6 Router Advertisements. Where a system is using DHCPv6 WAN type, devices on the same broadcast domain as that WAN can send crafted packets causing the system to lose IPv6 Internet connectivity.
- FreeBSD-SA-15:06.openssl: Multiple OpenSSL vulnerabilities. Most aren’t applicable, and worst impact is denial of service.
Zu den Bugfixen und Änderungen zählen Regeln für NAT, IPsec, DNS Forwarder/Resolver, Wireless, IPv6 und weitere. Interessant für IPSec ist die Aktualisierung von strongSwan auf 5.3.0, für Wireless wurde der Treiber für Atheros Drahtlos Netzwerkkarten auf die letzte Version die im FreeBSD enthalten ist, aktualisiert. Zudem wurde die Option für W-Lankarten vom Traffic Shaper entfernt, da hier aktuell noch kein Support vorliegt. Weitere sind z.B. der SSL Validation Cehck für Selfhost, Fehler im Traffic Shaping Wizard behoben, Text Cleanup sowie dem PHP Upgrade auf die Version 5.5.23.
Vollständige Liste der Bugfixe in pfSense Version 2.2.2
Security/Errata Notices
- FreeBSD-SA-15:09.ipv6: Denial of Service with IPv6 Router Advertisements. Where a system is using DHCPv6 WAN type, devices on the same broadcast domain as that WAN can send crafted packets causing the system to lose IPv6 Internet connectivity.
- FreeBSD-SA-15:06.openssl: Multiple OpenSSL vulnerabilities. Most aren’t applicable, and worst impact is denial of service.
Rules / NAT
- Added hidden config option to disable blocking of link-local IPv4 (169.254.0.0/16) for the rare instances where it’s required. Not recommended, violates RFC 3927.
- Fixed invalid ruleset generation when using port forwards with destination „any“ on a DHCP client WAN-type interface, have pure NAT mode reflection enabled, and have the interface with link up but unable to reach a DHCP server for an extended period. #4564
- Allow the use of version IPv4+IPv6 on firewall rules without restrictions on protocol. The former restrictions date back to earlier base software versions, and are no longer applicable.
- Omit route-to from rules specifying a specific gateway when that gateway is forced down. #4566
IPsec
- Enforce disabling of „prefer old SAs“ option. When the GUI configuration checkbox was removed in 2.2.1, it fell through to the default of the underlying software in many cases, leaving the option enabled instead of disabled. Having this option enabled will cause connectivity problems after rekeying in many circumstances. Upgrading to 2.2.2 will fix this.
- strongSwan upgraded to 5.3.0
- Don’t apply mobile IPsec phase 2 PFS configuration to non-mobile IPsec. #4538
- Correct applying of uniqueid configuration. #4359
- Bring back automatic exclusion of LAN subnet to LAN IP for scenarios where remote IPsec overlaps with local LAN subnet. #4504
- Enable ike_name for daemon logging, adding connection identifiers to IPsec logs that can be correlated to output of ‚ipsec statusall‘ (GUI log viewer integration to come).
DNS Forwarder/Resolver
- Fix DNS registration of hostname „0“ #4573
- Domain overrides to multiple server IPs are possible in DNS Resolver. Add message noting this, and how to achieve it. #4350
Wireless
- Atheros wireless driver updated to latest from FreeBSD 11-CURRENT. Not many changes since 2.2.1-RELEASE. #4582
- Wireless cards removed from ALTQ-capable interfaces (traffic shaper capability) since that isn’t supported at the moment. #4406
- New option „auto“ added for Standard. This omits configuring mode with ifconfig, which currently can trigger driver problems that don’t exist when not specified. Standard „auto“ is preferred, and possibly required, for BSS and IBSS wireless modes with Atheros cards (at a minimum, potentially others).
IPv6
- Make sure ‚DHCPv6 Prefix Delegation size‘ is provided if ‚Send IPv6 prefix hint‘ flag is checked to avoid generating invalid dhcp6c configuration file.
- DHCPv6 Relay fixed. #4572
- Allow „0“ for id-assoc na ID, id-assoc pd ID, sla-id and sla-len DHCP6 configuration options. #4547
- Fix the use of multiple prefixes in IPv6 router advertisements. #4468
Other
- Clean up logic in OpenVPN resync code. Discussion here and additional change here.
- SSL certificate validation disabled for selfhost – their certificate chain had a problem that made OpenSSL fail verification, making the service non-functional. #4545 The provider fixed the issue after 2.2.2-RELEASE, so verification has been re-enabled for 2.2.3 and newer.
- Fix error in traffic shaping wizard. #4529
- Fix broken image path. #4530
- A variety of minor text clean up in web interface.
- Remove some code no longer used in a few places.
- Clean up of code path when adding a new user. #4620
- Make sure RRD backup is not restored when /var memory disk is not in use. #4531
- PHP upgraded to 5.5.23
Link https://doc.pfsense.org/index.php/2.2.2_New_Features_and_Changes
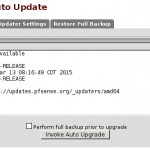
Das Update verläuft über den AutoUpdater recht unproblematisch. Ein Backup ist in jeden Fall zu empfehlen.
Interessiert in verschiedenste IT Themen, schreibe ich in diesem Blog über Software, Hardware, Smart Home, Games und vieles mehr. Ich berichte z.B. über die Installation und Konfiguration von Software als auch von Problemen mit dieser. News sind ebenso spannend, sodass ich auch über Updates, Releases und Neuigkeiten aus der IT berichte. Letztendlich nutze ich Taste-of-IT als eigene Dokumentation und Anlaufstelle bei wiederkehrenden Themen. Ich hoffe ich kann dich ebenso informieren und bei Problemen eine schnelle Lösung anbieten. Wer meinen Aufwand unterstützen möchte, kann gerne eine Tasse oder Pod Kaffe per PayPal spenden – vielen Dank.
