Der Spezialist für Securityprodukte, Sophos, hat die Modellreihe der UTM Firewall aktualisiert und bietet diese nun in Version 9.5 an. Zu den großen Neuerungen zählen:
- Verbesserungen in der WAF (Web Application Firewall)
- freie Wahl des Sophos Sandstorm Server Location
- UTM9 konfigurierbar über REST API
- Verbesserungen im Core / Base System
- Verbesesrungen im Management der UTM und dem Reporting

Das Update ist ca. 301MB groß und wird seit dem 9.5.2017 in 3 Phasen verteilt (Download, Verteilung auf die Server, Installation über Up2Date Funktion). Oder per FTP und direktem Upload in der UTM:
http://ftp.astaro.de/UTM/v9/up2date/u2d-sys-9.413004-500009.tgz.gpg
http://ftp.astaro.de/UTM/v9/up2date/u2d-sys-9.413004-500009.tgz.gpg.md5
Sophos UTM 9.5 Release Notes
WAF Enhancements
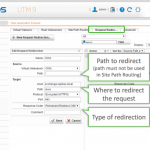
- WAF URL Redirection allows you to redirect traffic for a WAF protected URL to a different backend system or URL
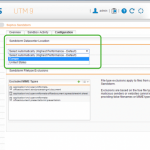
- WAF protection and authentication policy templates were added for common Microsoft services for protection and authentication
- Configure minimum allowed TLS version to improve security
- WAF Proxy Protocol Support to use the client IP info inside the ProxyProtocol header to make policy decisions and improve logging
- True File Type Scanning enables you to block uploads and downloads based on MIME type
Sophos Sandstorm
- Datacenter location selection option for Sophos Sandstorm without relying on DNS based location detection
- Sandstorm activity reporting expanded to include email attachments for improved visibility
- Scan exceptions for Sophos Sandstorm to exclude specific filetypes from being sent to Sophos Sandstorm analysis
Base System
- Download all UTM logs in a single archive
- Support Access with SSH is extending the existing Support Access feature
- 64-bit PostgreSQL Database to generate reports with big datasets faster. The existing database will be migrated without impacting any data.
- SNMP Monitoring of full filesystem to integrate UTM filesystem monitoring in regular SNMP based monitoring solutions
- Certificate Expiration Notification 30 days before expiration date via WebAdmin and e-Mail, giving you plenty of notice for certificate renewal
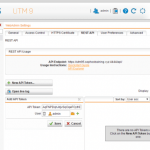
- RESTful API to configure Sophos UTM 9
Up2Date Information
News
- 9.5 Release
- Features
- WAF URL redirection
- WAF configurable TLS version
- WAF true file type detection
- WAF templates
- Sophos Sandstorm configuration of data center
- Sophos Sandstorm file exceptions
- RESTful API to configure UTM
- AWS CloudWatch Logs Agent
- 64-bit PostgreSQL database
- Email notification for expiring certificates
- Support Access for SSH
- SNMP monitoring of the file system
Remarks
- System will be rebooted
- Configuration will be upgraded
- Connected REDs will perform firmware upgrade
- Connected Wifi APs will perform firmware upgrade
Bugfixes
- NUTM-6646 [AWS] REST API panic when unlocking unlocked mutex
- NUTM-6657 [AWS] Configure AWS profiles via WebAdmin
- NUTM-6696 [AWS] Configure CloudWatch support via WebAdmin
- NUTM-6708 [AWS] Cloud update not working with conversion deployments
- NUTM-6814 [AWS] Rest API is accessible with default password if basic setup has not completed
- NUTM-6887 [AWS] REST API panic when inserting into node which is not of type array
- NUTM-7032 [AWS] SignalException not handled for SecurityGroupsManagement#update
- NUTM-7055 [AWS] queen_configuration_management / aws_resource_management SIGUSR1 handling
- NUTM-7056 [AWS] LocalJumpError
- NUTM-7057 [AWS] aws_set_sd_check AWS::EC2::Errors::RequestLimitExceeded
- NUTM-7061 [AWS] Connection refused – connect(2) for „localhost“ port 4472
- NUTM-3194 [Access & Identity] incorrect SSH logins trigger backend authentication requests
- NUTM-3222 [Access & Identity] RED10/50: DNS port open on WAN interfaces
- NUTM-3260 [Access & Identity] User Portal – IPsec Windows Support
- NUTM-4149 [Access & Identity] [RED] Use Sophos NTP pool servers
- NUTM-4323 [Access & Identity] NULL pointer deref in red_nl_cmd_tunnel_dump
- NUTM-4705 [Access & Identity] Don’t use DNS server from the RED branch as an ISP forwarder
- NUTM-4852 [Access & Identity] [RED] flock() on closed filehandle $fhi at /</var/confd/confd.plx>Object/itfhw/red_server.pm line 563.
- NUTM-4994 [Access & Identity] STAS creates users even if automatic user creation is disabled
- NUTM-5134 [Access & Identity] [OTP] User Portal should recommend Sophos Authenticator
- NUTM-5925 [Access & Identity] [RED] prevent configuration for VLAN for Split modes
- NUTM-6387 [Access & Identity] HTML5 VNC connection not disconnecting
- NUTM-6641 [Access & Identity] [OTP] user can select algorithm for automatic tokens
- NUTM-6668 [Access & Identity] [IPsec] L2TP/Cisco policy changes do not update ipsec.conf
- NUTM-6749 [Access & Identity] RED15w does not send split DNS traffic over RED tunnel
- NUTM-5965 [Basesystem] Sensors command on SG125w doesn’t show hardware fan RPM
- NUTM-6468 [Basesystem] BIND Security update (CVE-2016-9131, CVE-2016-9147, CVE-2016-9444)
- NUTM-6718 [Basesystem] Update NTP to 4.2.8p9
- NUTM-6846 [Basesystem] Linux kernel: ip6_gre: invalid reads in ip6gre_err() (CVE-2017-5897)
- NUTM-6847 [Basesystem] BIND Security update (CVE-2017-3135)
- NUTM-6902 [Basesystem] Linux kernel: ipv4 keep skb->dst around in presence of IP options (CVE-2017-5970)
- NUTM-7048 [Basesystem] Implement software workaround for Intel CPUs
- NUTM-7067 [Basesystem] Update OpenSSH to openssh-6.6p1
- NUTM-7370 [Basesystem] Bootsplash still shows 9.4 instead of 9.5
- NUTM-7653 [Basesystem] Internal SSL certification verification broken
- NUTM-5658 [Confd] Stripped restore unaccessable if default internal interface is removed
- NUTM-3062 [Email] Mails From mail spool gets quarantined because of „500 Max connection limit reached“ in cssd
- NUTM-4753 [Email] Support recipient verification with multiple AD servers
- NUTM-5350 [Email] Per user blacklist does not apply until smtp service restarts
- NUTM-5823 [Email] Scanner timeout or deadlock for all mails with a .scn attachment
- NUTM-5892 [Email] SMTP Exception doesn’t allow ‚&‘ sign within the email address
- NUTM-6135 [Email] DLP custom expression doesn’t get triggered if the email body contains certain strings
- NUTM-6355 [Email] Email not blocked with expression list
- NUTM-4474 [Kernel] Kernel panic – not syncing: Fatal exception in interrupt
- NUTM-6358 [Kernel] Kernel: unable to handle kernel NULL pointer dereference at 0000000000000018
- NUTM-4969 [Network] Uplink does not recover from error state
- NUTM-5314 [Network] 10gb SFP+ flexi module interface fails when under load
- NUTM-5428 [Network] Bridge interface can not acquire Dynamic IPv6 address correctly. This interface repeats up/down.
- NUTM-5831 [Network] Changing static IP on interface does not take effect immediately
- NUTM-5861 [Network] IPv4 static address gets deleted from confd (and WebAdmin) once IPv6 on the same interface fails to obtain dynamic address
- NUTM-6077 [Network] Static route on bridge interface disappears after rebooting the UTM
- NUTM-6807 [Network] SSL VPN not being redistributed into OSPF
- NUTM-6901 [Network] Eth0 is removed while configuring bridge interface
- NUTM-2420 [WAF] Remove session management from basic authentication
- NUTM-5603 [WAF] Issue with expired lifetime of WAF connections without any hint
- NUTM-5628 [WAF] WAF – Provide import and export options for HTTPS domain list
- NUTM-5640 [WAF] GUI issue when adding wildcard certificate into Virtual Webservers
- NUTM-6156 [WAF] UTM still fails scan for CVE-2016-2183 (SWEET32) after update to 9.408
- NUTM-6294 [WAF] WAF – Naming collisions for default profiles
- NUTM-6522 [WebAdmin] SMC Test failed after Settings are applied
- NUTM-6788 [WebAdmin] Add support for SG105W, SG135W and SG230 in WebAdmin
- NUTM-7337 [WebAdmin] Fix appliance picture for SG105w N9
- NUTM-6467 [Web] FTP connection fails when using transparent FTP Proxy
- NUTM-6732 [Web] Certificate issue with transparent Web Proxy – „unable to get local issuer certificate“
- NUTM-6876 [Web] Remove insecure RC4 from default cipher list for Web Protection HTTPS scanning on upgrade to 9.5 or restore of pre-9.5 backup
- NUTM-7586 [Web] Chrome v58 and higher fail verification with HTTPS scanning enabled
- NUTM-5638 [WiFi] RED15w – integrated AP isn’t shown as pending in transparent / split mode
- NUTM-5786 [WiFi] RED15w – if more then one SSID is configured only one is working correctly
- NUTM-6215 [WiFi] Issue when roaming between wireless with some clients
- NUTM-6335 [WiFi] VLAN fallback not working for integrated AP from RED15w
- NUTM-6448 [WiFi] AP55 stuck as inactive
- NUTM-6511 [WiFi] AP does not get IP address on 100 Mbit ethernet link
Interessiert in verschiedenste IT Themen, schreibe ich in diesem Blog über Software, Hardware, Smart Home, Games und vieles mehr. Ich berichte z.B. über die Installation und Konfiguration von Software als auch von Problemen mit dieser. News sind ebenso spannend, sodass ich auch über Updates, Releases und Neuigkeiten aus der IT berichte. Letztendlich nutze ich Taste-of-IT als eigene Dokumentation und Anlaufstelle bei wiederkehrenden Themen. Ich hoffe ich kann dich ebenso informieren und bei Problemen eine schnelle Lösung anbieten. Wer meinen Aufwand unterstützen möchte, kann gerne eine Tasse oder Pod Kaffe per PayPal spenden – vielen Dank.
