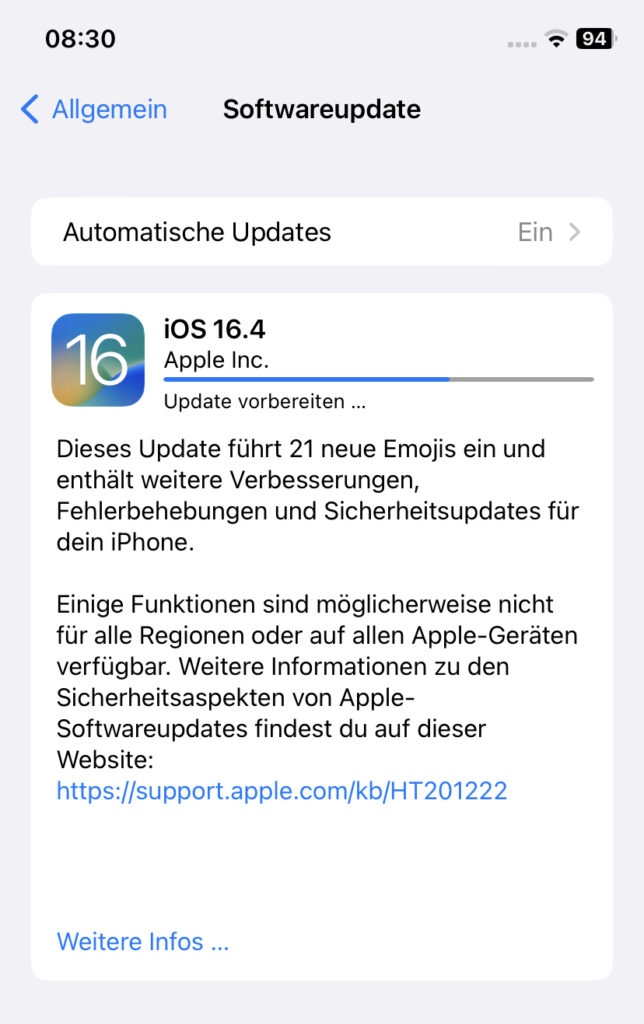
Apple hat das neue iOS und iPadOS 16.4 veröffentlicht. Inzwischen gibt es auch die Release Notes für die geschlossenen Sicherheitslücken. Diese betreffen u.a. die Apple Neural Engine, den Kalender, die Kamera, CarPlay, iCloud, Kernel, Safari, Fotos uvm.
Apple iOS 16.4 Security Changes
Accessibility
Available for: iPhone 8 and later, iPad Pro (all models), iPad Air 3rd generation and later, iPad 5th generation and later, and iPad mini 5th generation and later
Impact: An app may be able to access information about a user’s contacts
Description: A privacy issue was addressed with improved private data redaction for log entries.
CVE-2023-23541: Csaba Fitzl (@theevilbit) of Offensive Security
Apple Neural Engine
Available for: iPhone 8 and later, iPad Pro (all models), iPad Air 3rd generation and later, iPad 5th generation and later, and iPad mini 5th generation and later
Impact: An app may be able to execute arbitrary code with kernel privileges
Description: The issue was addressed with improved memory handling.
CVE-2023-23540: Mohamed GHANNAM (@_simo36)
CVE-2023-27959: Mohamed GHANNAM (@_simo36)
Apple Neural Engine
Available for: iPhone 8 and later, iPad Pro (all models), iPad Air 3rd generation and later, iPad 5th generation and later, and iPad mini 5th generation and later
Impact: An app may be able to execute arbitrary code with kernel privileges
Description: An out-of-bounds write issue was addressed with improved bounds checking.
CVE-2023-27970: Mohamed GHANNAM
Apple Neural Engine
Available for: iPhone 8 and later, iPad Pro (all models), iPad Air 3rd generation and later, iPad 5th generation and later, and iPad mini 5th generation and later
Impact: An app may be able to break out of its sandbox
Description: This issue was addressed with improved checks.
CVE-2023-23532: Mohamed Ghannam (@_simo36)
AppleMobileFileIntegrity
Available for: iPhone 8 and later, iPad Pro (all models), iPad Air 3rd generation and later, iPad 5th generation and later, and iPad mini 5th generation and later
Impact: A user may gain access to protected parts of the file system
Description: The issue was addressed with improved checks.
CVE-2023-23527: Mickey Jin (@patch1t)
AppleMobileFileIntegrity
Available for: iPhone 8 and later, iPad Pro (all models), iPad Air 3rd generation and later, iPad 5th generation and later, and iPad mini 5th generation and later
Impact: An app may be able to access user-sensitive data
Description: This issue was addressed by removing the vulnerable code.
CVE-2023-27931: Mickey Jin (@patch1t)
Calendar
Available for: iPhone 8 and later, iPad Pro (all models), iPad Air 3rd generation and later, iPad 5th generation and later, and iPad mini 5th generation and later
Impact: Importing a maliciously crafted calendar invitation may exfiltrate user information
Description: Multiple validation issues were addressed with improved input sanitization.
CVE-2023-27961: Rıza Sabuncu (@rizasabuncu)
Camera
Available for: iPhone 8 and later, iPad Pro (all models), iPad Air 3rd generation and later, iPad 5th generation and later, and iPad mini 5th generation and later
Impact: A sandboxed app may be able to determine which app is currently using the camera
Description: The issue was addressed with additional restrictions on the observability of app states.
CVE-2023-23543: Yiğit Can YILMAZ (@yilmazcanyigit)
CarPlay
Available for: iPhone 8 and later, iPad Pro (all models), iPad Air 3rd generation and later, iPad 5th generation and later, and iPad mini 5th generation and later
Impact: A user in a privileged network position may be able to cause a denial-of-service
Description: A buffer overflow was addressed with improved bounds checking.
CVE-2023-23494: Itay Iellin of General Motors Product Cyber Security
ColorSync
Available for: iPhone 8 and later, iPad Pro (all models), iPad Air 3rd generation and later, iPad 5th generation and later, and iPad mini 5th generation and later
Impact: An app may be able to read arbitrary files
Description: The issue was addressed with improved checks.
CVE-2023-27955: JeongOhKyea
Core Bluetooth
Available for: iPhone 8 and later, iPad Pro (all models), iPad Air 3rd generation and later, iPad 5th generation and later, and iPad mini 5th generation and later
Impact: Processing a maliciously crafted Bluetooth packet may result in disclosure of process memory
Description: An out-of-bounds read was addressed with improved bounds checking.
CVE-2023-23528: Jianjun Dai and Guang Gong of 360 Vulnerability Research Institute
CoreCapture
Available for: iPhone 8 and later, iPad Pro (all models), iPad Air 3rd generation and later, iPad 5th generation and later, and iPad mini 5th generation and later
Impact: An app may be able to execute arbitrary code with kernel privileges
Description: The issue was addressed with improved memory handling.
CVE-2023-28181: Tingting Yin of Tsinghua University
Find My
Available for: iPhone 8 and later, iPad Pro (all models), iPad Air 3rd generation and later, iPad 5th generation and later, and iPad mini 5th generation and later
Impact: An app may be able to read sensitive location information
Description: A privacy issue was addressed with improved private data redaction for log entries.
CVE-2023-23537: an anonymous researcher
FontParser
Available for: iPhone 8 and later, iPad Pro (all models), iPad Air 3rd generation and later, iPad 5th generation and later, and iPad mini 5th generation and later
Impact: Processing a maliciously crafted image may result in disclosure of process memory
Description: The issue was addressed with improved memory handling.
CVE-2023-27956: Ye Zhang of Baidu Security
Foundation
Available for: iPhone 8 and later, iPad Pro (all models), iPad Air 3rd generation and later, iPad 5th generation and later, and iPad mini 5th generation and later
Impact: Parsing a maliciously crafted plist may lead to an unexpected app termination or arbitrary code execution
Description: An integer overflow was addressed with improved input validation.
CVE-2023-27937: an anonymous researcher
iCloud
Available for: iPhone 8 and later, iPad Pro (all models), iPad Air 3rd generation and later, iPad 5th generation and later, and iPad mini 5th generation and later
Impact: A file from an iCloud shared-by-me folder may be able to bypass Gatekeeper
Description: This was addressed with additional checks by Gatekeeper on files downloaded from an iCloud shared-by-me folder.
CVE-2023-23526: Jubaer Alnazi of TRS Group of Companies
Identity Services
Available for: iPhone 8 and later, iPad Pro (all models), iPad Air 3rd generation and later, iPad 5th generation and later, and iPad mini 5th generation and later
Impact: An app may be able to access information about a user’s contacts
Description: A privacy issue was addressed with improved private data redaction for log entries.
CVE-2023-27928: Csaba Fitzl (@theevilbit) of Offensive Security
ImageIO
Available for: iPhone 8 and later, iPad Pro (all models), iPad Air 3rd generation and later, iPad 5th generation and later, and iPad mini 5th generation and later
Impact: Processing a maliciously crafted image may result in disclosure of process memory
Description: The issue was addressed with improved memory handling.
CVE-2023-23535: ryuzaki
ImageIO
Available for: iPhone 8 and later, iPad Pro (all models), iPad Air 3rd generation and later, iPad 5th generation and later, and iPad mini 5th generation and later
Impact: Processing a maliciously crafted image may result in disclosure of process memory
Description: An out-of-bounds read was addressed with improved input validation.
CVE-2023-27929: Meysam Firouzi (@R00tkitSMM) of Mbition Mercedes-Benz Innovation Lab and jzhu working with Trend Micro Zero Day Initiative
Kernel
Available for: iPhone 8 and later, iPad Pro (all models), iPad Air 3rd generation and later, iPad 5th generation and later, and iPad mini 5th generation and later
Impact: An app may be able to execute arbitrary code with kernel privileges
Description: A use after free issue was addressed with improved memory management.
CVE-2023-27969: Adam Doupé of ASU SEFCOM
Kernel
Available for: iPhone 8 and later, iPad Pro (all models), iPad Air 3rd generation and later, iPad 5th generation and later, and iPad mini 5th generation and later
Impact: An app with root privileges may be able to execute arbitrary code with kernel privileges
Description: The issue was addressed with improved memory handling.
CVE-2023-27933: sqrtpwn
LaunchServices
Available for: iPhone 8 and later, iPad Pro (all models), iPad Air 3rd generation and later, iPad 5th generation and later, and iPad mini 5th generation and later
Impact: Files downloaded from the internet may not have the quarantine flag applied
Description: This issue was addressed with improved checks.
CVE-2023-27943: an anonymous researcher, Brandon Dalton, Milan Tenk, and Arthur Valiev
LaunchServices
Available for: iPhone 8 and later, iPad Pro (all models), iPad Air 3rd generation and later, iPad 5th generation and later, and iPad mini 5th generation and later
Impact: An app may be able to gain root privileges
Description: This issue was addressed with improved checks.
CVE-2023-23525: Mickey Jin (@patch1t)
NetworkExtension
Available for: iPhone 8 and later, iPad Pro (all models), iPad Air 3rd generation and later, iPad 5th generation and later, and iPad mini 5th generation and later
Impact: A user in a privileged network position may be able to spoof a VPN server that is configured with EAP-only authentication on a device
Description: The issue was addressed with improved authentication.
CVE-2023-28182: Zhuowei Zhang
Photos
Available for: iPhone 8 and later, iPad Pro (all models), iPad Air 3rd generation and later, iPad 5th generation and later, and iPad mini 5th generation and later
Impact: Photos belonging to the Hidden Photos Album could be viewed without authentication through Visual Lookup
Description: A logic issue was addressed with improved restrictions.
CVE-2023-23523: developStorm
Podcasts
Available for: iPhone 8 and later, iPad Pro (all models), iPad Air 3rd generation and later, iPad 5th generation and later, and iPad mini 5th generation and later
Impact: An app may be able to access user-sensitive data
Description: The issue was addressed with improved checks.
CVE-2023-27942: Mickey Jin (@patch1t)
Safari
Available for: iPhone 8 and later, iPad Pro (all models), iPad Air 3rd generation and later, iPad 5th generation and later, and iPad mini 5th generation and later
Impact: An app may be able to unexpectedly create a bookmark on the Home Screen
Description: The issue was addressed with improved checks.
CVE-2023-28194: Anton Spivak
Sandbox
Available for: iPhone 8 and later, iPad Pro (all models), iPad Air 3rd generation and later, iPad 5th generation and later, and iPad mini 5th generation and later
Impact: An app may be able to bypass Privacy preferences
Description: A logic issue was addressed with improved validation.
CVE-2023-28178: Yiğit Can YILMAZ (@yilmazcanyigit)
Shortcuts
Available for: iPhone 8 and later, iPad Pro (all models), iPad Air 3rd generation and later, iPad 5th generation and later, and iPad mini 5th generation and later
Impact: A shortcut may be able to use sensitive data with certain actions without prompting the user
Description: The issue was addressed with additional permissions checks.
CVE-2023-27963: Jubaer Alnazi Jabin of TRS Group Of Companies, and Wenchao Li and Xiaolong Bai of Alibaba Group
TCC
Available for: iPhone 8 and later, iPad Pro (all models), iPad Air 3rd generation and later, iPad 5th generation and later, and iPad mini 5th generation and later
Impact: An app may be able to access user-sensitive data
Description: This issue was addressed by removing the vulnerable code.
CVE-2023-27931: Mickey Jin (@patch1t)
WebKit
Available for: iPhone 8 and later, iPad Pro (all models), iPad Air 3rd generation and later, iPad 5th generation and later, and iPad mini 5th generation and later
Impact: Processing maliciously crafted web content may bypass Same Origin Policy
Description: This issue was addressed with improved state management.
WebKit Bugzilla: 248615
CVE-2023-27932: an anonymous researcher
WebKit
Available for: iPhone 8 and later, iPad Pro (all models), iPad Air 3rd generation and later, iPad 5th generation and later, and iPad mini 5th generation and later
Impact: A website may be able to track sensitive user information
Description: The issue was addressed by removing origin information.
WebKit Bugzilla: 250837
CVE-2023-27954: an anonymous researcher
Quelle: About the security content of iOS 16.4 and iPadOS 16.4 – Apple Support
Interessiert in verschiedenste IT Themen, schreibe ich in diesem Blog über Software, Hardware, Smart Home, Games und vieles mehr. Ich berichte z.B. über die Installation und Konfiguration von Software als auch von Problemen mit dieser. News sind ebenso spannend, sodass ich auch über Updates, Releases und Neuigkeiten aus der IT berichte. Letztendlich nutze ich Taste-of-IT als eigene Dokumentation und Anlaufstelle bei wiederkehrenden Themen. Ich hoffe ich kann dich ebenso informieren und bei Problemen eine schnelle Lösung anbieten. Wer meinen Aufwand unterstützen möchte, kann gerne eine Tasse oder Pod Kaffe per PayPal spenden – vielen Dank.